

Most ebook files are in PDF format, so you can easily read them using various software such as Foxit Reader or directly on the Google Chrome browser.
Some ebook files are released by publishers in other formats such as .awz, .mobi, .epub, .fb2, etc. You may need to install specific software to read these formats on mobile/PC, such as Calibre.
Please read the tutorial at this link: https://ebookbell.com/faq
We offer FREE conversion to the popular formats you request; however, this may take some time. Therefore, right after payment, please email us, and we will try to provide the service as quickly as possible.
For some exceptional file formats or broken links (if any), please refrain from opening any disputes. Instead, email us first, and we will try to assist within a maximum of 6 hours.
EbookBell Team
4.7
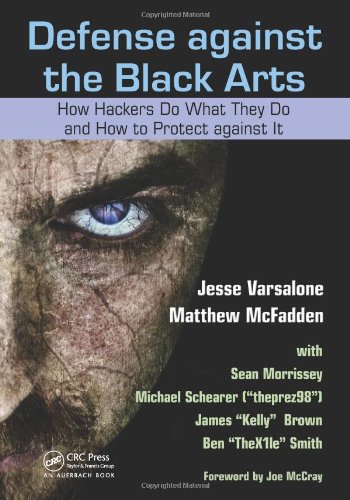
76 reviewsAs technology has developed, computer hackers have become increasingly sophisticated, mastering the ability to hack into even the most impenetrable systems. The best way to secure a system is to understand the tools hackers use and know how to circumvent them. Defense against the Black Arts: How Hackers Do What They Do and How to Protect against It provides hands-on instruction to a host of techniques used to hack into a variety of systems.
Exposing hacker methodology with concrete examples, this book shows you how to outwit computer predators at their own game. Among the many things you’ll learn:
The book profiles a variety of attack tools and examines how Facebook and other sites can be used to conduct social networking attacks. It also covers techniques utilized by hackers to attack modern operating systems, such as Windows 7, Windows Vista, and Mac OS X. The author explores a number of techniques that hackers can use to exploit physical access, network access, and wireless vectors. Using screenshots to clarify procedures, this practical manual uses step-by-step examples and relevant analogies to facilitate understanding, giving you an insider’s view of the secrets of hackers.